Automated Security Testing


Why Our Security Testing Services?
Advantages of Automated Security Testing Services
Industries We Work With
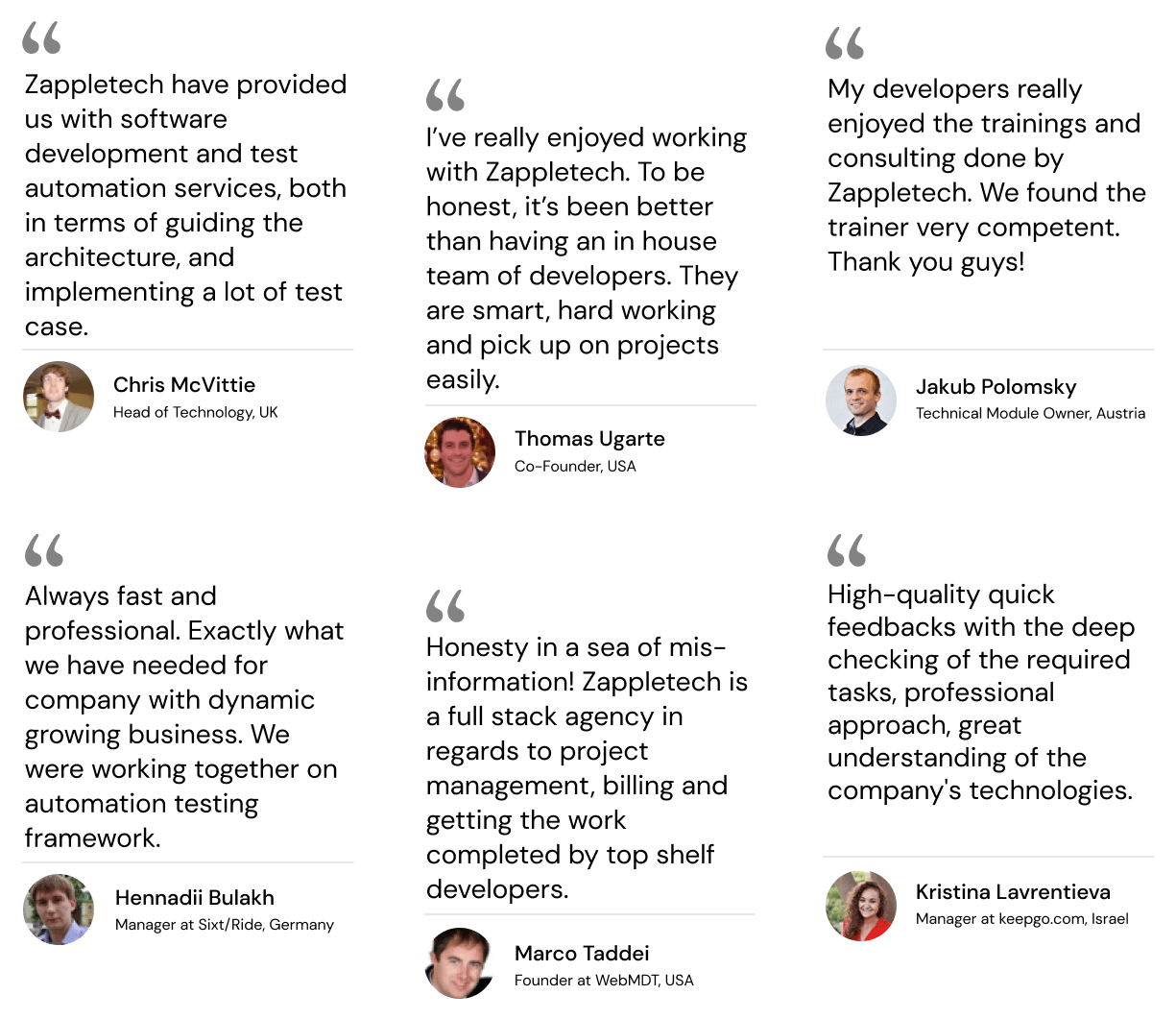
What Our Customers Say
We Provide the Following Security Testing Types
Examples of Security Testing Scenarios
Our Expertise

How We Work
Start Cooperation Now!
Why Should You Choose Automated Security Testing?
Automated security is a proactive approach to security testing that utilizes specialized tools and technologies to automate the process of identifying vulnerabilities, detecting potential threats, and assessing overall security posture. Unlike traditional manual testing methods, which rely on human testers to manually execute test cases and identify vulnerabilities, automated security testing automates the entire testing process, from test case generation to result analysis.
Principles and Methodologies
At its core, automated testing is grounded in security test automation, efficiency, and accuracy. By automating repetitive tasks and leveraging machine learning algorithms, automated testing enables organizations to identify vulnerabilities and security weaknesses more quickly and accurately than ever before. This proactive approach to security testing helps organizations identify and remediate potential security issues before they can be exploited by malicious actors, reducing the risk of data breaches and other security incidents.
The methodologies behind automated security testing vary depending on the tools and technologies used. However, some common methodologies include:
Static Analysis involves analyzing an application’s source code or binary code to identify potential security vulnerabilities. Static analysis tools scan the code for known security issues and coding errors that attackers could exploit.
Dynamic Analysis: Also known as black-box testing, dynamic analysis involves testing an application while running to identify potential security vulnerabilities. Dynamic analysis tools simulate real-world attack scenarios to identify security weaknesses and vulnerabilities in the application’s runtime environment.
Interactive Application Security Testing (IAST): IAST combines static and dynamic analysis elements by instrumenting the application code to monitor for security vulnerabilities while the application is running. IAST tools provide real-time feedback on potential security issues, allowing developers to quickly identify and remediate vulnerabilities.
Types of Automated Security Testing Tools
Various types of security testing tools are available, each designed to address specific aspects of security testing. Some common types of security testing tools include:
Vulnerability Scanners: These tools scan networks, systems, and applications for known vulnerabilities and security weaknesses. They automate the process of identifying and prioritizing vulnerabilities, enabling organizations to assess their security posture quickly and take appropriate remediation actions.
Penetration Testing Tools: Penetration testing tools simulate real-world cyber attacks to identify potential security vulnerabilities and weaknesses in an organization’s systems and applications. These tools automate penetration tests, enabling organizations to identify and remediate security issues before attackers can exploit them.
Security Configuration Management Tools: These tools automate configuring and managing security settings and configurations across an organization’s IT infrastructure. They help organizations ensure that their systems and applications are configured securely and comply with industry best practices and regulatory requirements.
By leveraging these various types of security testing tools, organizations can enhance the efficiency and effectiveness of their security testing efforts. They can identify vulnerabilities and security weaknesses more quickly and accurately and reduce the risk of data breaches and other security incidents.
Advantages of Automated Security Testing
Security testing offers numerous advantages over traditional manual testing methods, making it an invaluable asset in today’s rapidly evolving cybersecurity landscape.
Efficiency and Scalability | Automated security testing has an important benefit of speeding up and scaling in more ways. Security test automation with repetitive tasks and technology are known to speed up and improve testing of processes. Security testing can be done more seamlessly, regularly, and efficiently above the manpower limitations. This approach flatters organizations to conduct large-scale security testing frequently, which helps their systems stay secure, as cyber threats are never the same as they previously were. |
Consistency and Repeatability | Another significant point that highlights the advantages of automated security testing is its repeatability and accuracy. Compared with manual testing, which is always subjective and prone to human error, automatic testing can eliminate the chance of error. Every time the tests are executed, they are done consistently and accurately. Comprehensive risk assessment makes it easier to identify weaknesses, including vulnerabilities in an organization’s security, leading to more reliable and robust security systems. |
Cost-Effectiveness | Security testing not only provides prompt results but is also economical in that it will save you time and money in the long run. Although an investment category may come within the sphere of implementing automated testing tools and technologies, its productivity and scalability over time may cause cost savings. Manual interventions can be prevented by automated security, which, in return, streamlines and saves time and resources. Organizations can then use these freed-up resources to devote to other parts of the program as they wish. |
Early Detection of Vulnerabilities | One of the most significant advantages of security testing is its ability to detect vulnerabilities early in the development lifecycle. By integrating security testing into the development process and automating the testing of code changes as they are made, organizations can identify and remediate vulnerabilities before attackers can exploit them. This proactive approach to security testing helps organizations reduce the risk of data breaches and other security incidents, ultimately enhancing their overall security posture. |
In summary, security testing offers numerous advantages over traditional manual testing methods, including increased efficiency and scalability, consistency and repeatability, cost-effectiveness, and early detection of vulnerabilities. By leveraging the power of security test automation and advanced analytics, organizations can enhance the effectiveness of their security testing efforts and better protect their systems and data from cyber threats.
Implementing Automated Security Testing
Implementing security testing into the development lifecycle requires careful planning, coordination, and integration with existing processes. While the benefits of security testing are substantial, successful implementation requires overcoming common challenges and ensuring seamless integration with development workflows.
Steps to Integrate Automated Testing into the Development Lifecycle
- Assessment and Planning: Begin by assessing the organization’s current security testing practices and identifying areas where automation can benefit most. Develop a comprehensive plan outlining the automated security testing initiative’s goals, objectives, and scope.
- Tool Selection: Evaluate automated testing tools and technologies to determine which best meet the organization’s needs and requirements. Consider factors such as compatibility with existing systems, ease of use, scalability, and cost-effectiveness.
- Integration with Development Processes: Integrate security testing into the organization’s existing development processes, such as continuous integration/continuous deployment (CI/CD) pipelines. Automate the execution of security tests as part of the build and deployment process to ensure that security is baked into every development lifecycle stage.
- Training and Education: Provide development teams with training and education on how to use automated testing tools effectively. Ensure that developers understand the importance of security testing and how it fits into the overall development process.
- Continuous Improvement: Continuously monitor and evaluate the effectiveness of security testing practices. Collect feedback from development teams and stakeholders to identify areas for improvement and refine testing processes accordingly.
Overcoming Common Challenges in Implementation
Implementing automated security testing may encounter several challenges, including:
- Resistance to Change: Some team members may resist adopting automated testing practices due to a fear of job displacement or a lack of familiarity with new tools and technologies. Addressing these concerns through training, education, and clear communication is essential.
- Technical Complexity: Integrating automated testing into existing development processes can be technically complex, particularly in large IT environments. Organizations may need additional resources and expertise to overcome technical challenges and ensure successful implementation.
- Resource Constraints: Limited resources, such as budget, time, and skilled personnel, can pose significant challenges to implementing security testing initiatives. Prioritize resource allocation based on the organization’s priorities and objectives to maximize the effectiveness of automated testing efforts.
Best Practices for Automated Security Testing
Implementing security testing is not just about deploying tools; it requires a strategic approach and adherence to best practices to maximize effectiveness and efficiency. Here are some key best practices for security testing:
Establishing Clear Objectives and Criteria
Before starting the security test automation of security testing, it is important to create a strategic plan and metrics for the success of the testing strategy. Outline the goals of the testing program, which can be – enumerating and finding loopholes, implementing standards, and protecting the organization’s data. Create measurable success metrics, e.g., the number of wards tracked down and resolved, a drop in an incident of security, or improvement in security metrics.
Selecting the Right Tools and Technologies
Choosing the right tools and technologies is essential for the success of security testing initiatives. Evaluate different automated security testing tools based on functionality, scalability, ease of use, compatibility with existing systems, and cost-effectiveness. Consider your organization’s specific needs and requirements, as well as the types of applications and systems being tested, when selecting tools and technologies.
Integrating Security Testing into DevOps Practices
Security testing completes with DevOps practices and security pruners the mental capacity of the whole software development lifecycle. Integrate the security testing tools and procedures into the existing CI/CD pipeline to have security testing performed as part of the development and deployment process on an automated basis. It follows that security is forcefully promoted across the development phases rather than being an afterthought. The effect is that security vulnerabilities are remedied initially and will likely not make their way into the production environment.
Continuously Updating and Refining Testing Processes
Security threats and vulnerabilities are constantly evolving, so it’s essential to continuously update and refine your security testing processes to adapt to new challenges. Regularly review and update your testing methodologies, tools, and technologies to incorporate the latest security best practices and address emerging threats. Collect feedback from development teams, security experts, and stakeholders to identify areas for improvement and refine testing processes accordingly.
By following these best practices, organizations can maximize the effectiveness and efficiency of their security testing initiatives, improve their overall security posture, and better protect their systems and data from cyber threats. Automated security testing is a powerful tool for enhancing security, but it requires careful planning, strategic implementation, and ongoing refinement to realize its full potential.
Challenges and Limitations of Automated Security Testing
While security testing offers numerous benefits, it also presents several challenges and limitations that organizations must address to maximize effectiveness and efficiency.
False Positives and Negatives
One of the primary challenges of security testing is the potential for false positives and negatives. False positives occur when a security testing tool incorrectly identifies a non-existent vulnerability as a security issue, leading to wasted time and resources investigating and remedying the false positive. Conversely, false negatives occur when a security testing tool fails to identify a genuine vulnerability, leaving the organization vulnerable to potential security breaches. Mitigating false positives and negatives requires careful tuning of testing tools and manual verification and validation of test results by security experts.
Complexity of Certain Systems and Applications
The complexity of certain systems and applications can pose significant challenges for automated security testing. Legacy systems, custom-built applications, and complex architectures may not be well-suited to automated testing tools, leading to incomplete or inaccurate test results. Additionally, some applications may rely on technologies or frameworks not easily supported by automated testing tools, further complicating the testing process. Addressing the complexity of systems and applications requires combining technical expertise, specialized tools, and creative problem-solving to ensure comprehensive test coverage.
Skills Gap and Training Requirements
Implementing automated testing requires skilled personnel proficiently using testing tools and technologies effectively. However, organizations often have a skills gap, with a shortage of qualified security professionals with expertise in automated testing methodologies. Additionally, existing staff may require training and education to develop the necessary skills and knowledge to successfully implement and manage automated testing initiatives. Addressing the skills gap and training requirements may require investing in employee training programs, hiring external consultants, or partnering with third-party vendors with expertise in automated security.
Regulatory Compliance Issues
Organizations operating in regulated industries, such as finance, healthcare, and government, must comply with various regulatory requirements governing data security and privacy. Automated security testing can help organizations identify and remediate security vulnerabilities to comply with regulations such as PCI DSS, HIPAA, GDPR, etc. However, automated testing tools must be configured and used to align with regulatory requirements, such as ensuring the protection of sensitive data during testing and maintaining audit trails of test results. Failure to address regulatory compliance issues can result in severe penalties, fines, and reputational damage for organizations.
In summary, while security testing offers numerous benefits for organizations seeking to enhance their security posture, it also presents several challenges and limitations that must be addressed. By understanding and mitigating these challenges, organizations can maximize the effectiveness and efficiency of their automated testing initiatives and better protect their systems and data from cyber threats.
Conclusion
Automation of security testing forms an armada against cyber risks, built precisely to help organizations fight with available options and offer protection in the modern digital world. As we have explored this topic, we have deepened our understanding of the vital role that security testing plays in the current data protection context, given the fast pace at which digital threats evolve. The alternative conventional approach, which once used to be essential, now gets barriers when the modern is out.
The introduction of automatic security testing is full of consequences. Not only is it the beginning of a new era in the field of information security, but it is also a first step in providing organizations with engagement of its security procedures at the highest level. Applying security test automation to the workflow allows you to build robust scalability according to approved standards and practices and minimize the budget spent on security testing. Additionally, the chances of early detection of flaws made possible by automation are undoubtedly proactive means to investigate upcoming breaches and thus protect your assets and data.
Although the path to drama-free automated security testing is not without hurdles, one thing is for certain. Struggles with false positives and negatives, the complexity of multiple environments and products, an absence of appropriate skills, and regulatory hurdles that have to be overcome require governments to make sound choices and do their best to help. However, the sheer facing of these issues can continue to be hindered through an unflinching spirit and approach of optimal strategies, which offer a road to effective security testing mechanisms.
Hereby, there is no doubt that automatic security testing introduction is a turning point that makes it possible to increase the effectiveness of any software and decrease the risk of a data breach. By identifying tangible objectives, selecting the precise kit, integrating it in DevOps processes, and improving it continuously, organizations will exploit security testing and ensure the safety of their systems and data against new types of cyber threats. With such stakes, adopting automated testing will remain essential in creating a more stable and adaptive security paradigm to cope with the fast-changing threat landscape.
Frequently Asked Questions:
What are the types of security testing?
- Vulnerability Scanning
- Security Scanning
- Penetration testing
- Risk Assessment
- Security Auditing
- Ethical hacking
- Posture Assessment
What is security testing in AQA?
Security testing is a procedure for identifying faults in an information system’s security measures so that data is protected and the system’s functioning is maintained as intended. Security testing ensures that particular security criteria are satisfied, much as software or service requirements must be met in AQA.
How do you use security testing?
The basic purpose of security testing is to find and measure potential vulnerabilities in a system so that attacks can be encountered and the system does not stop working or be exploited. It also aids in the detection of all potential security vulnerabilities in the system, as well as assisting developers in the resolution of issues through coding.
Why is security testing used?
The basic purpose of security testing is to find and measure potential vulnerabilities in a system so that attacks can be encountered and the system does not stop working or be exploited.








